

Update (May 2026): tfsec is no longer actively maintained. Aqua Security merged the tfsec check library into Trivy in 2024, and no new checks or features are being added. For current IaC scanning guidance, see Checkov vs Trivy in 2026: IaC Scanning After tfsec and Terrascan.
In this section of the IaC Scanning Tools Guide, we will be looking at tfsec and discussing the benefits, key features, and looking at some real world examples. You can explore the other parts of this guide below.
Jump to section:
- What is an IaC scan tool?
- What is Checkov?
- What is Terrascan?
- Comparing Checkov vs. tfsec vs. Terrascan
What is tfsec?
tfsec is a security scanner for your Terraform code. It performs static analysis of your code and detects potential misconfigurations that could lead to security risks. It supports multiple cloud providers, such as AWS, Azure, and GCP, and has hundreds of built-in rules. It also allows you to define your own custom rules using Rego policies or JSON/YAML custom policies. You can run tfsec locally or in your CI pipelines, and get developer-friendly output in various formats. tfsec is an open-source project backed by Aqua Security that aims to help you secure code in your IaC.
Benefits and Key Features of using tfsec
Some benefits and key features of using tfsec are:
| Feature | Details |
|---|---|
| Scanning IaC | Yes for security and compliance before deployment |
| IaC Frameworks Supported | Only Terraform |
| Reporting | Detailed reports and recommendations for fixing the detected issues in different formats such as text, JSON, CSV, Checkstyle, JUnit, and SARIF. |
| Integrations | Many tools including GitHub Actions, GitLab CI, and VS Code |
| Policy Customizations | Yes using JSON or YAML |
| Open-source | Yes |
| Example of Issues that can be detected | Insecure use of plain text secrets or hard-coded credentials Misconfigured network access rules or firewall settings Unencrypted data storage or communication Missing or outdated security features or patches Non-compliance with industry standards or regulations |
How to get started with tfsec
How to install tfsec?
There are several ways to install tfsec on your system. You can use a package manager such as brew (for macOS or Linux), choco (for Windows), or scoop (for Windows). You can also download the binary for your system from the releases page on GitHub. Alternatively, you can install tfsec with Go using the command:
go install github.com/aquasecurity/tfsec/cmd/tfsec@latest
If you don't want to install tfsec on your system, you can also run it in a Docker container using the command:
docker run --rm -it -v "$(pwd):/src" aquasec/tfsec /src
If you follow along with our GitHub repo using Codespaces, it will be installed for you.
How to use tfsec?
To use tfsec, you simply need to run it on a directory that contains your Terraform code. For example:
tfsec ./Terraform
By default, tfsec will use a lovely output format that shows the severity, description, location, and resolution of each problem. You can change the output format using the --format flag.
For example:
tfsec ./Terraform --format json
This will output the results in JSON format. You can also use other formats such as csv, checkstyle, junit, sarif, text, markdown, html, and gif.
You can also customize the behavior of tfsec using various flags or a configuration file. For example, you can exclude certain checks using the --exclude flag. You can also enable or disable colors, force exit codes, ignore warnings or errors, set custom paths for modules or policies, and more. For a full list of flags you can run tfsec -h
Example use cases of tfsec
Use case 1: Scan your Terraform code for security issues before applying it
One of the most common use cases of tfsec is to scan your Terraform code for security issues before applying it to your cloud environment. This way, you can catch and fix any problems before they cause any damage or expose any vulnerabilities.
Let’s scan the same folder we scanned with checkov. Run the following commands:
tfsec ./Terraform
This will scan all the Terraform files in the current directory and print out a report of any issues found. For example:
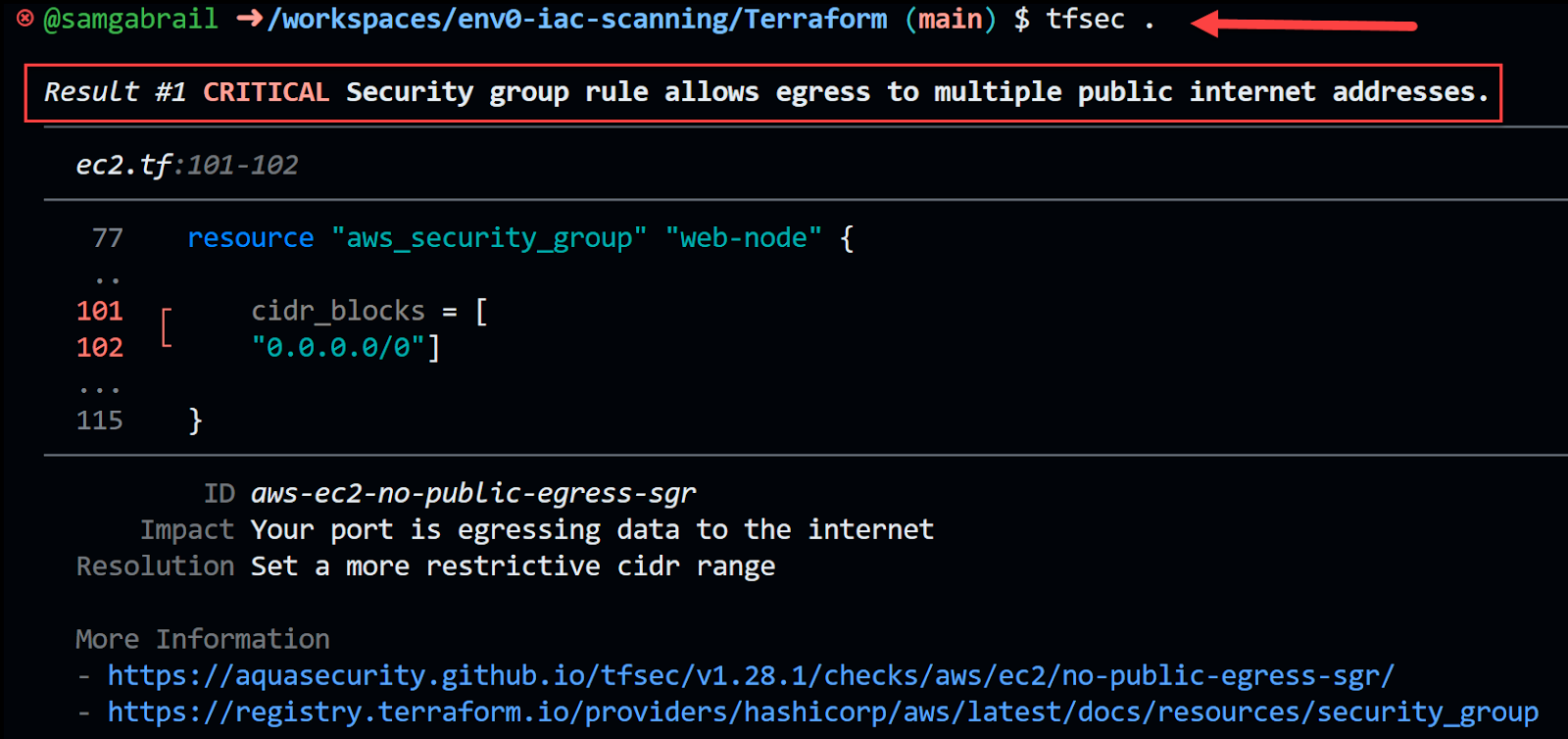
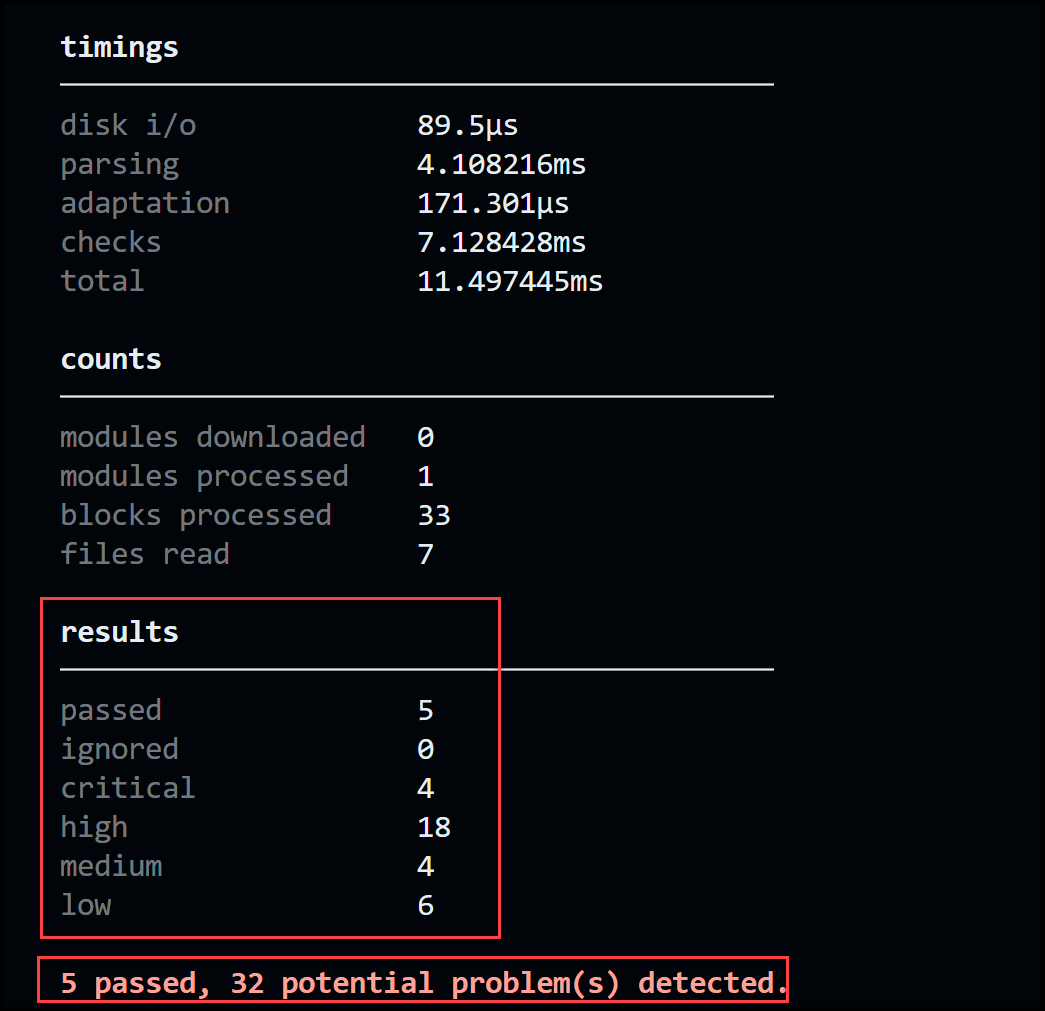
As you can see, tfsec provides a clear and concise output that shows the location, severity, and description of each issue. It also provides a link to the documentation page where you can learn more about the issue and how to fix it.
Use case 2: Scan your Kubernetes manifests
Unfortunately, tfsec does not support scanning Kubernetes manifests. It was built specifically to scan Terraform files.
tfsec Custom Policies
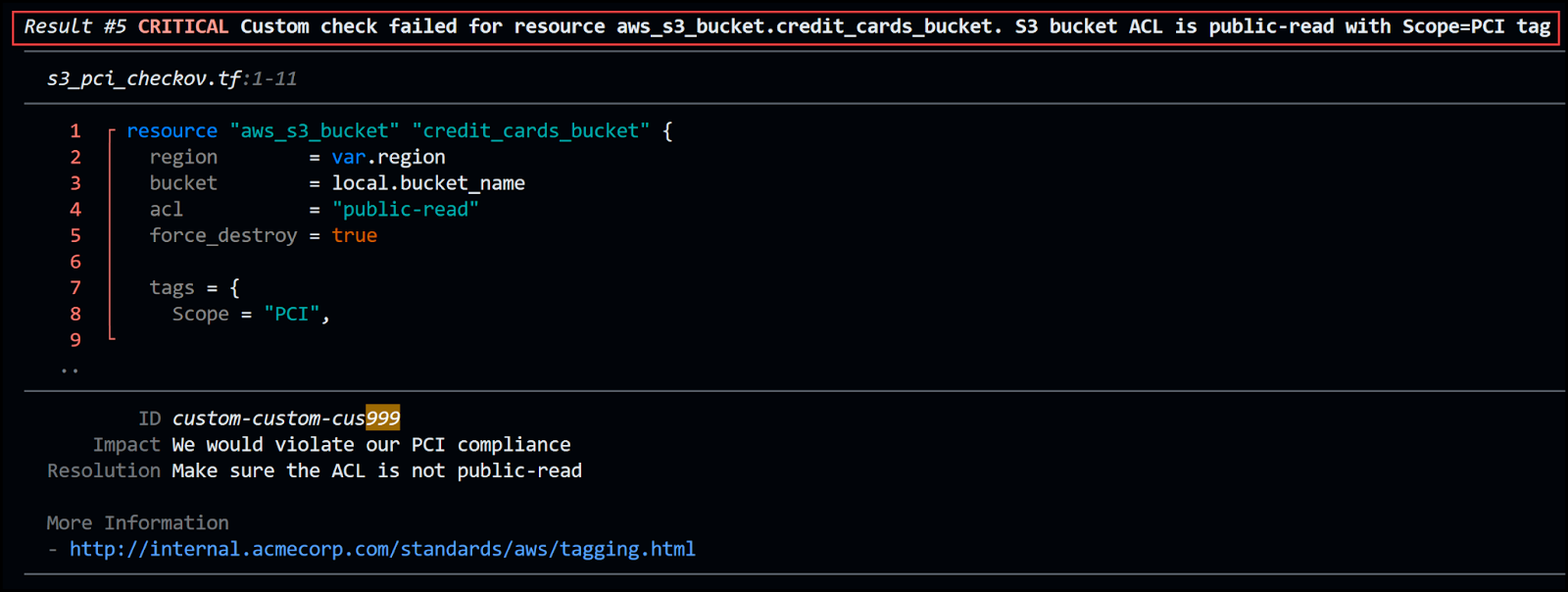
Similar to checkov, you can create custom checks in tfsec either using YAML or JSON or using Rego. Let’s create a check similar to the one we did with checkov. We shouldn’t allow an S3 bucket’s ACL to be public-read when it is tagged with the key Scope and the value of PCI.
Custom checks are defined as JSON files or YAML files which sit in the .tfsec folder in the root check path. Any file with the suffix tfchecks.json or tfchecks.yaml will be parsed and the checks included during the run.
Check the pci_policy_tfchecks.yaml in the .tfsec folder in our repo. Below is the content:
---
checks:
- code: CUS999
description: Make sure S3 bucket ACL is NOT public-read if it has a Scope=PCI tag
impact: We would violate our PCI compliance
resolution: Make sure the ACL is not public-read
requiredTypes:
- resource
requiredLabels:
- aws_s3_bucket
severity: CRITICAL
matchSpec:
action : or
predicateMatchSpec :
- action : notContains
name : tags
value:
Scope: "PCI"
- action : notContains
name : acl
value: public
errorMessage: S3 bucket ACL is public-read with Scope=PCI tag
relatedLinks:
- http://internal.acmecorp.com/standards/aws/tagging.html
Use the normal command to run:
tfsec ./Terraform
And examine the output:

.webp)



![Using Open Policy Agent (OPA) with Terraform: Tutorial and Examples [2026]](https://cdn.prod.website-files.com/63eb9bf7fa9e2724829607c1/69d6a3bde2ffe415812d9782_post_th.png)
